Single Sign-On (SSO)
For security reasons (e. g. due to
phishing),
IT Services is continuously expanding the use of single sign-on (log on once
and be identified in every connected system) or single sign-in (log on to the
same - known - page for every system) for the central
web-based systems;
users should only enter their password in one place and react very attentively
if they are asked to enter their password on other pages.
Although we are also aware of the risks - for example, there is no uniform
solution for a "single log-out" and the individual systems can have
valid sessions of different lengths (i. e. in one system you might stay
logged in for 8 hours and in another only 2) - we have decided to use SSO
with
auth.tugraz.at and in the final development there should be only
this solution for central services - as far as technically possible.
sso.tugraz.at will be used for
federated services only
(like participating in the
ubook offer).
Implemented is SSO for sso.tugraz.at with Shibboleth (an extension
of the SAML standard) and for auth.tugraz.at with OpenID Connect
(an extension of OAuth2).
Our central services will leave the sessions open for 14 hours,
only after that a new login will be forced, other systems can - as mentioned
above - also set other times or force a new login (i. e. single sign-in)
at all, we cannot influence that centrally.
TUGRAZonline actively warns about the end of the session.
For security reasons, our SSO solutions have been extended with a
2-factor authentication from
privacyIDEA, i. e. after logging in with username and password,
another window appears in which a one-time password (6 digits) must be entered.
Alternatively, one can continue to log in to the SSO system with the
ID
Austria (also a 2-factor solution).
appears in which a one-time password (6 digits) must be entered.
Alternatively, one can continue to log in to the SSO system with the
ID
Austria (also a 2-factor solution).
However, since - if you are logged in to one tab, in other tabs - you can enter
all SSO applications without logging in, it is strongly recommended to take one
of the following measures when leaving the computer without shutting it down:
- Activate screen lock (with secure password).
- Log off.
If you are not sure if the logout is only local:
call logout.tugraz.at (see below).
- Close browser.
All web applications are called directly as before - regardless of whether they
are integrated into the SSO system or not. So the SSO page itself never has to
be called directly, the participating web applications redirect to the SSO page
if required and this - after checking the authentication - redirects back to
the desired web application.
In other words: There is no central login page where you log in e. g.
in the morning. Only if an authentication is really necessary, you will then
be redirected to one of our SSO pages
(sso.tugraz.at /
auth.tugraz.at
/
auth.tugraz.at ).
The two systems are largely independent, i. e. a logout in one system
does not cause a logout in the other system, even logout.tugraz.at
only works on systems where you have logged in via auth.tugraz.at!)
and after logging in (or if you are already logged in: immediately) you are
redirected back to the calling system.
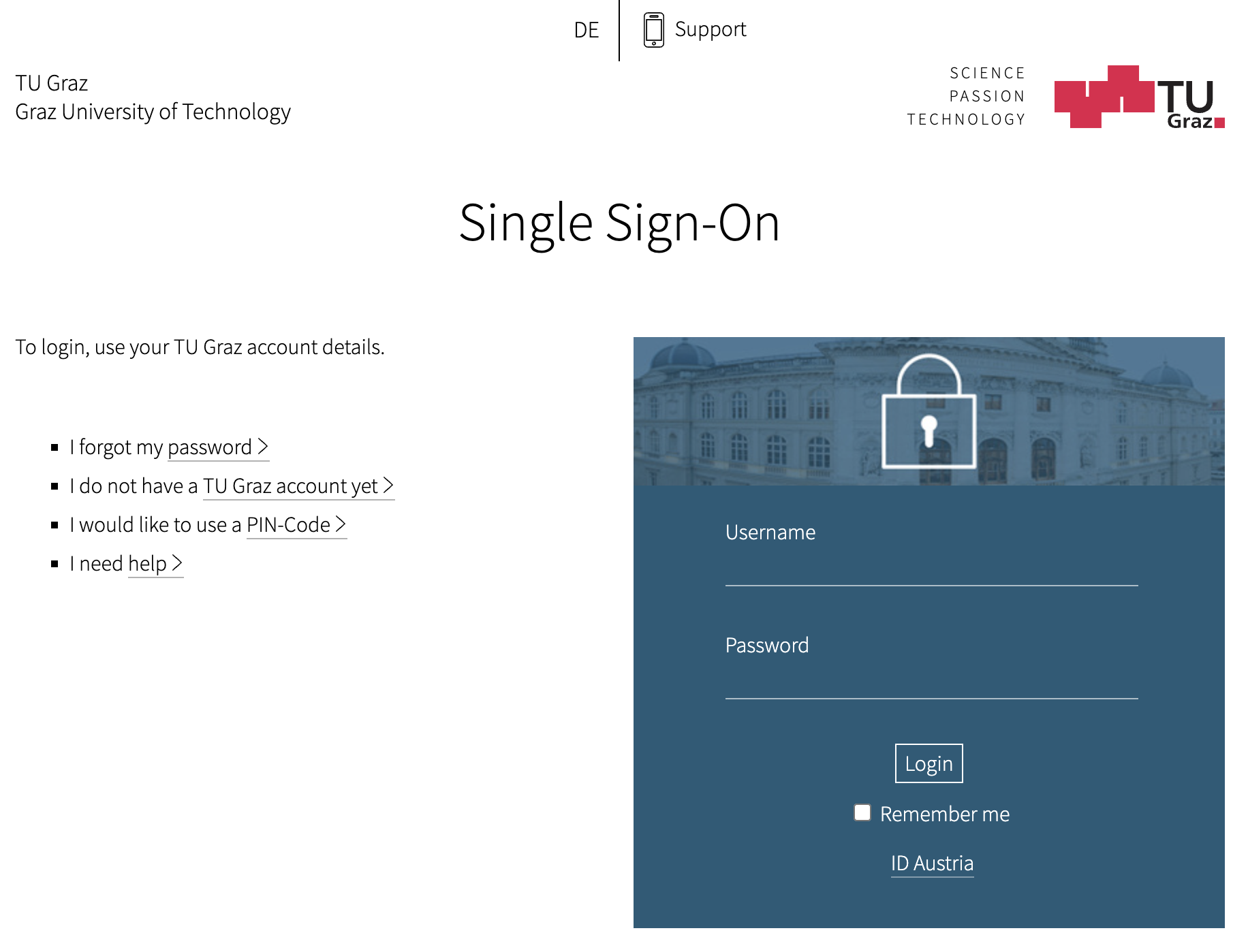
In auth.tugraz.at you can use the item "Remember me" to prevent the
session from being ended when the browser is closed, but the maximum session duration is not affected either. However, as this can be
a security issue, you should only activate this on biometrically secured
devices.
).
The two systems are largely independent, i. e. a logout in one system
does not cause a logout in the other system, even logout.tugraz.at
only works on systems where you have logged in via auth.tugraz.at!)
and after logging in (or if you are already logged in: immediately) you are
redirected back to the calling system.
In auth.tugraz.at you can use the item "Remember me" to prevent the
session from being ended when the browser is closed, but the maximum session duration is not affected either. However, as this can be
a security issue, you should only activate this on biometrically secured
devices.
The application then checks whether you are authorized to use the application.
Central systems that are (still) accessible from the Internet without SSO/2FA
(
hellgrau … in Umsetzung)
- ivpn.tugraz.at - VPN-Lösung für Institute der TU Graz
- rds-webaccess.tugraz.at - das RDS-System (Terminal Service) der TU Graz;
alle von dort erreichbaren Systeme sind mit einem 2. Faktor geschützt.
If you know a web-based system that is not secured by SSO and that is not
in this list, but that asks you for the TU Graz password: Please do not enter
your access data, it could be a phishing
site.
Please report such systems to us: Even if they are not phishing sites,
question why they do not switch to SSO or why the site is not listed here!
|
Logout - Single log-out (SLO)